
David Colombo, a 19-year-old security researcher, claims to have access to over 25 Tesla vehicles in 13 countries, thanks to a software flaw in the company’s systems. Thankfully, he is in contact with Tesla’s security team right now to get things patched, otherwise nefarious actors would be able to remotely run commands, such as disabling Sentry Mode, opening doors or windows, and even starting keyless driving. Read more for a video and additional information.

Ring security footage from a home in the UK shows two car thieves using a keyless entry hack to steal a 2019 Tesla Model S in under 30 seconds. They used a technique called the relay attack where a box and its wires are used to detect if the vehicle keyfob is nearby, and if so, the signal is copied and transmitted to the second person standing next to the car.
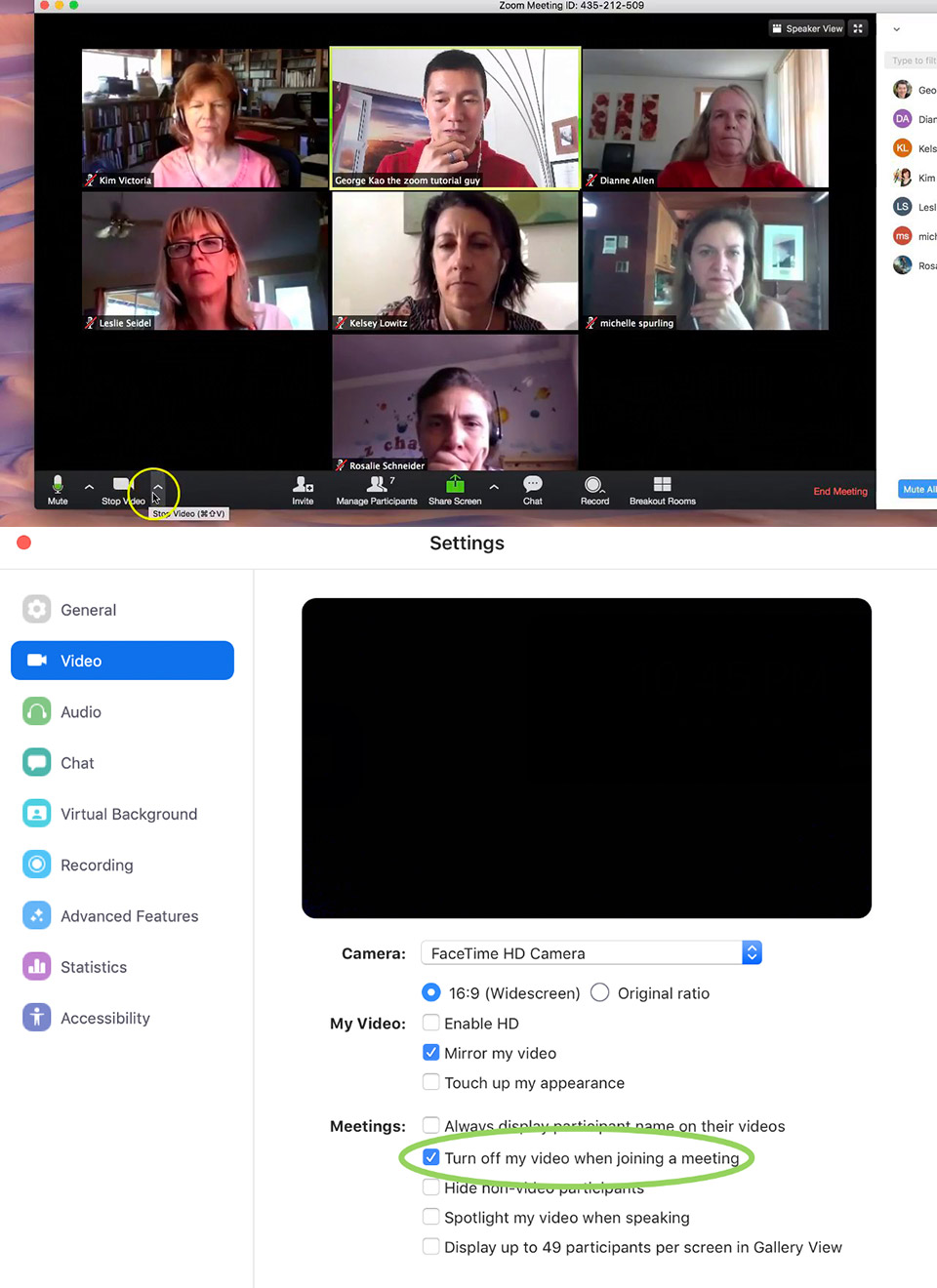
Photo credit: George Kao | Jonathon Leitschuh
Security researcher Jonathan Leitschuh discovered a zero-day vulnerability for the Zoom video conferencing app on Macs and publicly disclosed it today. Simply put, any website can open a video-enabled call on a Mac with the Zoom app installed because the software automatically installs a web server on OS X systems that accepts requests regular browsers wouldn’t. A website would simply be able to “forcibly join a user to a Zoom call, with their video camera activated, without the user’s permission.” This also means that even if you uninstall Zoom, the web server can reinstall the software without requiring manual approval. Read more of a screenshot of what one person encountered when trying it.

Computer security researchers at Trend Micro have discovered a new way hackers are trying to run .EXE files, the official executable file format used for Windows, on macOS. During their investigation, these .EXE files were delivering a malicious payload that overrides Mac’s built-in protection mechanisms such as Gatekeeper, with the highest numbers for infections to be in the United Kingdom, Australia, Armenia, Luxembourg, South Africa and the United States. It was found in the installer of a popular firewall app for Mac and Windows called Little Snitch, available for download from various torrent websites.

Computer security researcher Linus Henze discovered a KeySteal exploit in macOS Mojave that enables anyone to steal passwords from the operating system’s Keychain Access without requiring administrator privileges. Fortunately, it doesn’t affect items stored in iCloud’s keychain, or as far as we know. This may take a while to get patched, since Henze is protesting Apple’s bug bounty program, which only pays out to researchers for disclosing bugs on iOS and not macOS. Read more for a video of the exploit in-action.

Photo credit: Instagram via Buzzfeed
Let’s face it, Apple’s AirPods are quite easy to lose, especially if you don’t put them back in their charging case immediately after use. Gabrielle Reilly, a 22-year-old paralegal from Virgina, has come up with an interesting solution. Now one place you might not want to wear Airings is at the airport, as the TSA security check might cause some issues.
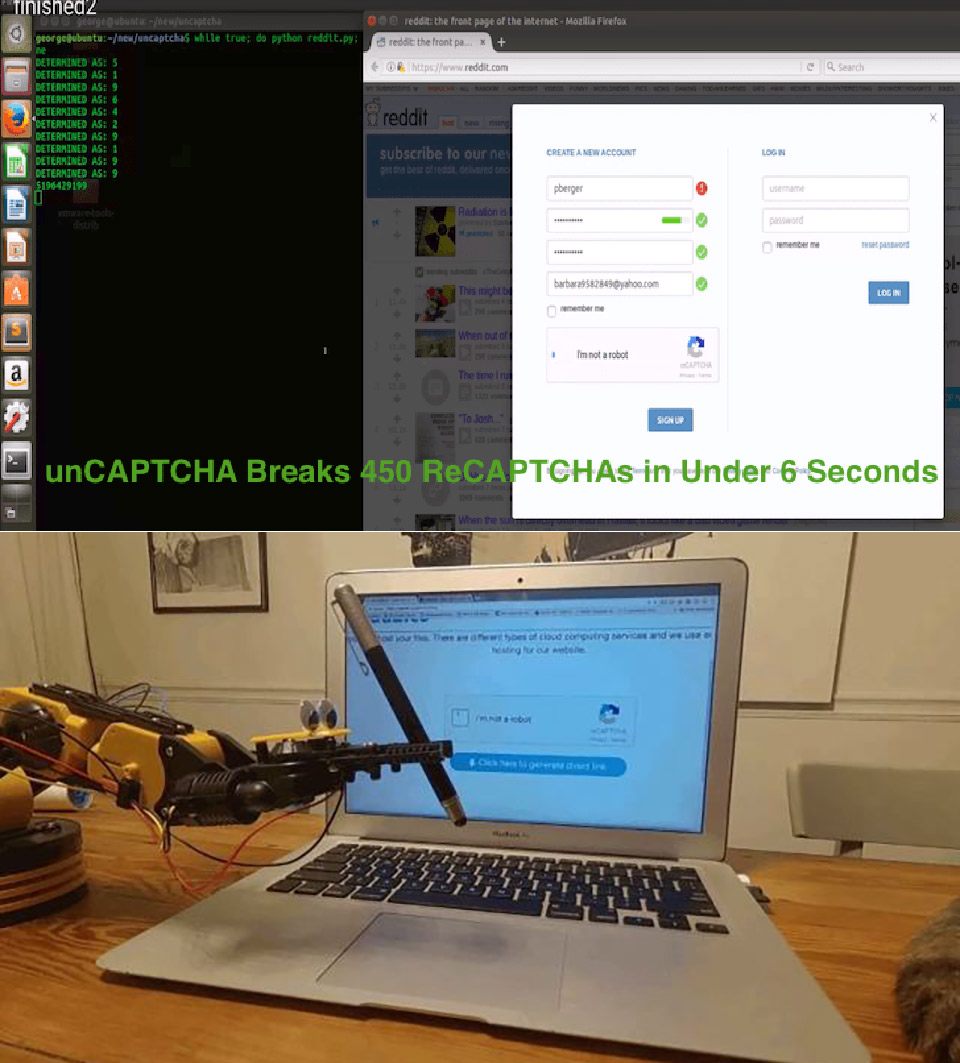
The AI-powered unCAPTCHA system designed by University of Maryland reseachers can now defeat Google’s latest audio-based reCAPTCHA challenges with 90% accuracy. Simply put, the unCAPTCHA system downloads the audio challenge, splits it into several clips, then runs them through several text-to-speech systems to determine exact and near-homophones, weighing the aggregate results by confidence level before sending the most probable answer back to Google.

Photo credit: BBC
Sam Curry, an 18-year-old student in Omaha, Nebraska, has tinkered with computers from a young age, but not in the way most use them. As a sophomore in high school, he found a way into the system that allowed him to pose as an administrator, meaning that he could have changed student grades, but Sam just wanted to enter the network as a prank. Subsequently when school administrators found out, he was suspended for two weeks. The next time he discovered a security vulnerability, he reported the bug to the high school administration instead of exploiting it, and received a $50 gift card to Subway as a reward. Since that time, he’s earned more than $100,000 from legally hacking well known institutions including the U.S. Department of Defense, Valve, and Yahoo. Read more for a video interview and additional information.

Sony’s PlayStation Classic was heavily criticized for using the European versions of the 20 included games, mainly because they’re slower due to the PAL television standard, which has a refresh rate of 50 Hz. Now, the miniature console has been hacked to run the games that should have came loaded with it. Since the device is basically an ARM-powered mini PC running an open-source emulator, BleemSync (or gpghax) lets you run any PS1 game you want off a USB drive. This software modifies the PlayStation Classic’s game database to enable one to swap out games with new ones. Simply put, the steps involve modifying the console’s database file to add your desired game(s), load that on a pen drive and then copy your desired game(s) onto it. Read more for another video tutorial and additional information.

Sony’s PlayStation Classic may not have lived up to the hype, but for those who did pick one up, there’s at least one hidden Easter egg that we know of, and it’s fairly easy to access. Simply plug in just a compatible USB keyboard (Apple, Logitech and Razer keyboards confirmed to be incompatible), press the ESC button, and you’ll be greeted with hidden settings menus. These reveal a few things about the miniature console, including that it runs the open-source PCSX ReARMed emulator as well giving users the ability to change the video output mode, complete with scan lines, and the option of playing the games using an analog controller. Read more for a full video review and additional information.




