Photo credit: George Kao | Jonathon Leitschuh
Security researcher Jonathan Leitschuh discovered a zero-day vulnerability for the Zoom video conferencing app on Macs and publicly disclosed it today. Simply put, any website can open a video-enabled call on a Mac with the Zoom app installed because the software automatically installs a web server on OS X systems that accepts requests regular browsers wouldn’t. A website would simply be able to “forcibly join a user to a Zoom call, with their video camera activated, without the user’s permission.” This also means that even if you uninstall Zoom, the web server can reinstall the software without requiring manual approval. Read more of a screenshot of what one person encountered when trying it.
This Zoom vulnerability is bananas. I tried one of the proof of concept links and got connected to three other randos also freaking out about it in real time. https://t.co/w7JKHk8nZy pic.twitter.com/arOE6DbQaf
— Matt Haughey (@mathowie) July 9, 2019
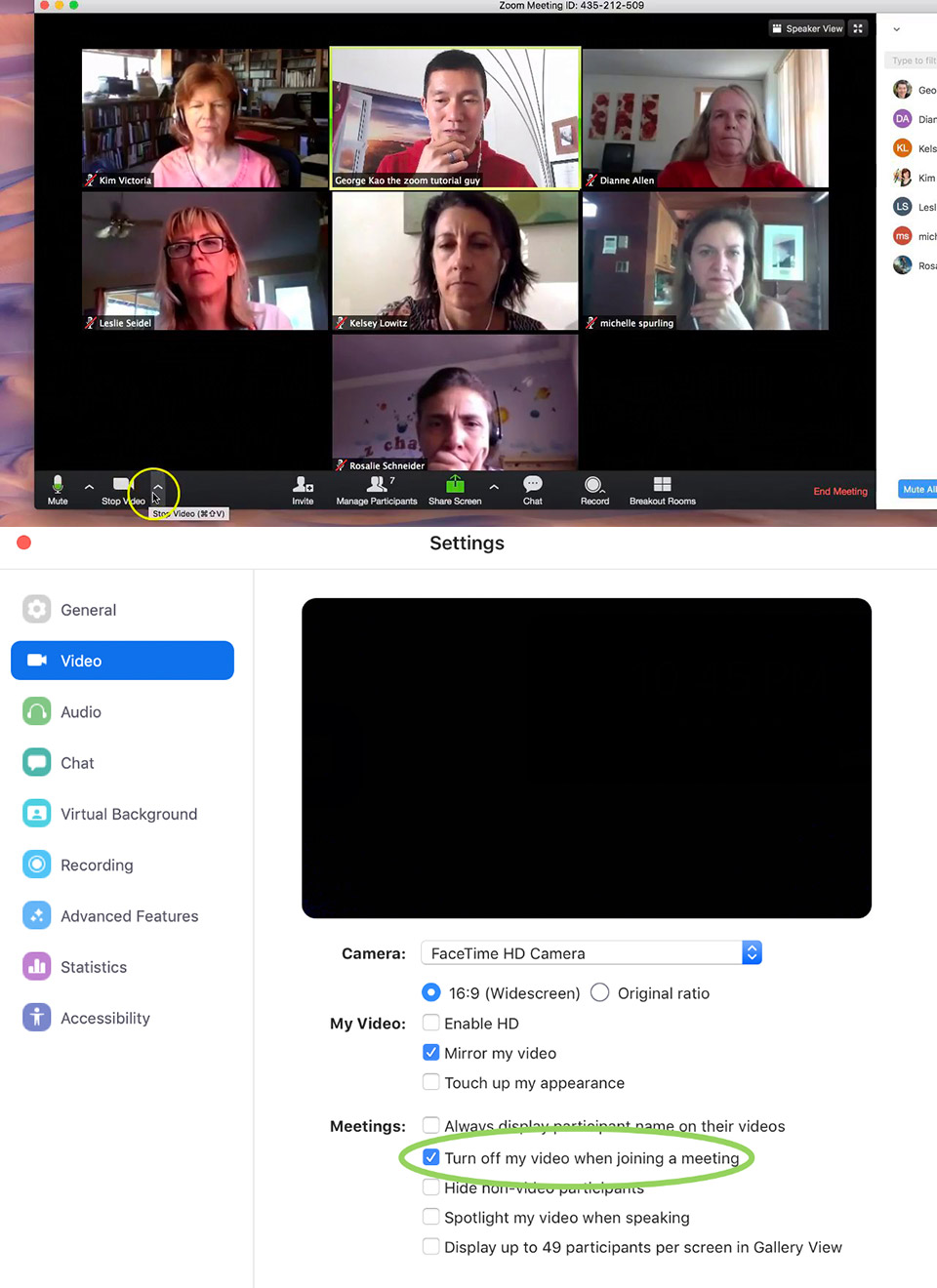
Like all responsible security researchers, Leitschuh disclosed this vulnerability to Zoom back in late March to give them 90 days to fix the issue, but unfortunately, their team hasn’t prioritized it. Fortunately, you’re able to patch this yourself, by going into Video –> Settings and checking “Turn off my video when joining a meeting.” The best course of action would be for Zoom to enable auto-update for all of its software and patch these zero-day vulnerabilities as they are reported.



